Attacking a website is not a straightforward process where you start randomly typing and suddenly have access to the system. Before exploiting a vulnerability, you have to actually find the vulnerability. The first part of attacking a system is information gathering. There are a lot of excellent tools out there for information gathering like Maltego or Nmap. Even a simple Google search can give you lots of useful information. After compiling a list of targets to focus on, you can start scanning those targets for vulnerabilities that can potentially be exploited. This is where Nikto comes in.
Nikto is an Open Source (GPL) web server scanner which performs comprehensive tests against web servers for multiple items, including over 6700 potentially dangerous files/programs, checks for outdated versions of over 1250 servers, and version specific problems on over 270 servers. It also checks for server configuration items such as the presence of multiple index files, HTTP server options, and will attempt to identify installed web servers and software (cirt.net/Nikto2).
Installing nikto
Nikto is Perl based and can run on almost any operating system with a Perl interpreter installed.
Installation of Nikto on Ubuntu 18.04 is pretty straightforward as the package is available on the default repositories. Perl is already installed on Ubuntu 18.04 by default. Therefore, you can simply use apt-get install nikto to install Nikto. You can also get Nikto from its Github.
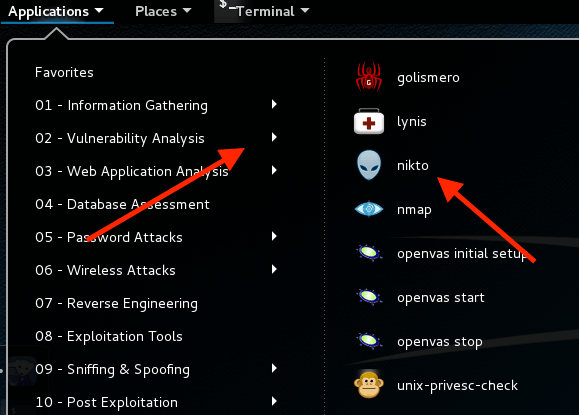
If you’re using Kali Linux, Nikto should come preinstalled. You can find it in the “Vulnerability Analysis” category.
The bare minimum
In its basic functionality, Nikto only requires you to specify the target host. The host can be either an IP address for a local service, a web domain to attack, an SSL/HTTPS website, or a list of different hosts. The target host can be specified with the -h or -host option.
nikto -h <IP or hostname>
If lucky, a basic scan like this can already reveal some useful information about the target or even find a vulnerability with a weaponized exploit.
Advanced scan options
Scanning an SSL-enabled website
Nikto is also capable of scanning an SSL enabled website.
If we know it’s an SSL site that we’re targeting, we can specify it in Nikto to save some time on the scan by adding -ssl to the end of the command.
nikto -h <IP or hostname> -ssl
For example, let’s run a scan on rangeforce.com to see what types of information a Nikto scan will show.
nikto -h rangeforce.com -ssl
- Nikto v2.1.6
---------------------------------------------------------------------------
+ Target IP: 34.94.195.177
+ Target Hostname: rangeforce.com
+ Target Port: 443
---------------------------------------------------------------------------
+ SSL Info: Subject: /OU=Domain Control Validated/OU=PositiveSSL Multi-Domain/CN=rangeforce.com
Altnames: rangeforce.com, blog.rangeforce.com, www.rangeforce.com
Ciphers: ECDHE-RSA-CHACHA20-POLY1305
Issuer: /C=GB/ST=Greater Manchester/L=Salford/O=Sectigo Limited/CN=Sectigo RSA Domain Validation Secure Server CA
+ Start Time: 2019-10-22 10:29:34 (GMT0)
---------------------------------------------------------------------------
+ Server: nginx/1.14.0 (Ubuntu)
+ Uncommon header 'x-runtime' found, with contents: 0.004264
+ Uncommon header 'x-request-id' found, with contents: f0498d9d-4503-40f3-971e-550fddf5b781
+ The site uses SSL and the Strict-Transport-Security HTTP header is not defined.
+ The site uses SSL and Expect-CT header is not present.
+ Root page / redirects to: https://rangeforce.com/home
+ Cookie _rfweb_session created without the secure flag
+ No CGI Directories found (use '-C all' to force check all possible dirs)
+ Multiple index files found: /index.php5, /index.php, /index.php7, /index.aspx, /index.html, /index.asp, /index.do, /index.jsp, /index.cfm, /index.php4, /index.htm, /index.pl, /index.cgi, /index.shtml, /default.asp, /index.php3, /index.jhtml, /default.htm, /default.aspx
+ Cookie request_method created without the secure flag
+ Cookie request_method created without the httponly flag
+ OSVDB-3092: /demo/: This might be interesting...
+ OSVDB-3092: /home/: This might be interesting...
+ Cookie _userhub_session created without the secure flag
+ 7791 requests: 0 error(s) and 11 item(s) reported on remote host
+ End Time: 2019-10-22 11:43:33 (GMT0) (4439 seconds)
----------------------------------------------------------------
After it connects to port 443, we see that there’s some useful information about the cipher. There’s also a list of other details like: the server is Nginx, the secure and httponly flags are not set for some cookies.
There’s also some items with an OSVDB prefix. Those listings represent vulnerabilities reported in the Open Source Vulnerability Database. Although the site has been shut down, you may find additional information about the vulnerability using this CVE reference tool.
There aren’t any major results from our scan that could be exploited.
Specifying the scan
You can specify the type of checks you want to run on the target with the -Tuning option. So if you only want to perform a Denial of Service test, then you can run:
nikto -Tuning 6 -h <IP or hostname>
Or maybe you would like to check everything except for SQL Injection:
nikto -Tuning x 9 -h <IP or hostname>
Here are all of the test types from the man page:
-Tuning
Tuning options will control the test that Nikto will use against a
target. By default, if any options are specified, only those tests
will be performed. If the "x" option is used, it will reverse the
logic and exclude only those tests. Use the reference number or
letter to specify the type, multiple may be used:
0 - File Upload
1 - Interesting File / Seen in logs
2 - Misconfiguration / Default File
3 - Information Disclosure
4 - Injection (XSS/Script/HTML)
5 - Remote File Retrieval - Inside Web Root
6 - Denial of Service
7 - Remote File Retrieval - Server Wide
8 - Command Execution / Remote Shell
9 - SQL Injection
a - Authentication Bypass
b - Software Identification
c - Remote Source Inclusion
x - Reverse Tuning Options (i.e., include all except specified)
The given string will be parsed from left to right, any x
characters will apply to all characters to the right of the
character.
Saving results
There is also an option to save your scan results to a file with the -output flag. You can specify the type of the output with the -Format option.
To save the scan results to a file called res.html:
nikto -output res.html -Format htm -h <IP or hostname>
False positives
Nikto is checking hundreds of URL’s for the presence of old scripts, vulnerable applications and other problems. This can sometimes result in many false positives if the detection of 404 -> 200 is not discovered by Nikto.
It is not difficult to spot as you will receive a great deal of invalid urls as positives. These are easily checked manually to ensure they are actual false positives.
For example, if most of the items in the scan result refer to a vulnerable file in the application, like this:
+ /site.pem: Potentially interesting archive/cert file found.
+ /site.pem: Potentially interesting archive/cert file found. (NOTE: requested by IP address).
This means that the application is configured to return status code 200 for every request, without actually ever delivering a file. Nikto is interpreting these 200 status codes to mean that the file it is requesting actually exists, which in the context of our application is a false positive.
We can eliminate such requests by disabling a Nikto plugin called sitefiles to see better where actual vulnerabilities might exist. You can achieve that by using the -Plugins option.
nikto -Plugins "@@DEFAULT;-sitefiles" -h <IP or hostname>
Here is the list of plugins used by Nikto.
Scanning traces
Nikto is by no means a stealthy tool. It will make thousands of requests to the web server, creating a large number of entries in the web server log files. This noise is actually an excellent way to test an in place Intrusion Detection System (IDS) or an attack detection ruleset like CRS that is used in the application firewall.
Sample entries made by a Nikto scan in an Nginx log:
192.168.6.1 - - [24/Oct/2019:19:34:52 +0000] "GET /moadmin/wu-moadmin.php HTTP/1.1" 404 27 "-" "Mozilla/5.00 (Nikto/2.1.6) (Evasions:None) (Test:007012)"
192.168.6.1 - - [24/Oct/2019:19:34:52 +0000] "GET /moadmin.php HTTP/1.1" 404 27 "-" "Mozilla/5.00 (Nikto/2.1.6) (Evasions:None) (Test:007012)"
192.168.6.1 - - [24/Oct/2019:19:34:52 +0000] "GET /wu-moadmin.php HTTP/1.1" 404 27 "-" "Mozilla/5.00 (Nikto/2.1.6) (Evasions:None) (Test:007012)"
192.168.6.1 - - [24/Oct/2019:19:34:52 +0000] "GET /phpmoadmin/moadmin.php HTTP/1.1" 404 27 "-" "Mozilla/5.00 (Nikto/2.1.6) (Evasions:None) (Test:007012)"
By using the -useragent option to override the default User-Agent, it is possible to evade firewall rules that detect requests from scanners by inspecting the User-Agent header.
Changing the User-Agent to Mozilla/5.00:
nikto -useragent Mozilla/5.00 -h <IP or hostname>
Sample log entries after changing the User-Agent:
192.168.6.1 - - [24/Oct/2019:20:01:05 +0000] "GET /moadmin/wu-moadmin.php HTTP/1.1" 404 27 "-" "Mozilla/5.00"
192.168.6.1 - - [24/Oct/2019:20:01:05 +0000] "GET /moadmin.php HTTP/1.1" 404 27 "-" "Mozilla/5.00"
192.168.6.1 - - [24/Oct/2019:20:01:05 +0000] "GET /phpmoadmin/moadmin.php HTTP/1.1" 404 27 "-" "Mozilla/5.00"
192.168.6.1 - - [24/Oct/2019:20:01:05 +0000] "GET /wu-moadmin/moadmin.php HTTP/1.1" 404 27 "-" "Mozilla/5.00"
Despite changing the User-Agent, a correctly configured web server log monitoring tool, host based intrusion detection system (HIDS) or network based intrusion detection system (NIDS) should still detect a Nikto scan.
Conclusion
Nikto is an awesome vulnerability scanning tool that is being regularly updated to provide reliable results even on the latest vulnerabilites. It is very easy to use, as the scan does not require much tweaking to discover useful information that can later be used for deeper exploitation or vulnerability assessment.
This blog post should only serve as an introduction to Nikto. There are much more possibilities in terms of scanning options, results and integrating scans with other tools. You can find more detailed information about this tool on cirt.net/Nikto2.

