It does not matter if you are a security engineer, a network administrator or even a cyber-criminal, tools for monitoring network traffic are the key to your success. With a detailed view of the numerous packets traversing a network, one can ascertain a lot about the security condition of that network. Network monitoring tools are also a vital resource for troubleshooting network performance problems. One very popular tool in this category is Wireshark.
Wireshark
Wireshark is a widely used network protocol analyzer that enables users to see what’s happening on their network at a detailed level. A free, open source tool, it is used by many IT and network operations teams in commercial enterprises, non-profit organizations, government agencies, and educational institutions. As an active open source project, Wireshark benefits from the development efforts of volunteer contributors around the world. More information is available at (wireshark.org)
The Wireshark interface is divided into three main areas: packet list, packet details and packet bits. Additionally, the user is provided with a display filter that he or she can use to customize the display according to their needs or preferences. The details pane presents the protocols and protocol fields of the selected packet. By expanding the selection, the user can apply individual filters. By selecting a specific portion of the packet bits, the corresponding section will be highlighted in the packet details pane and vice versa. Any byte that does not encode a printable ASCII character is instead represented by a period.
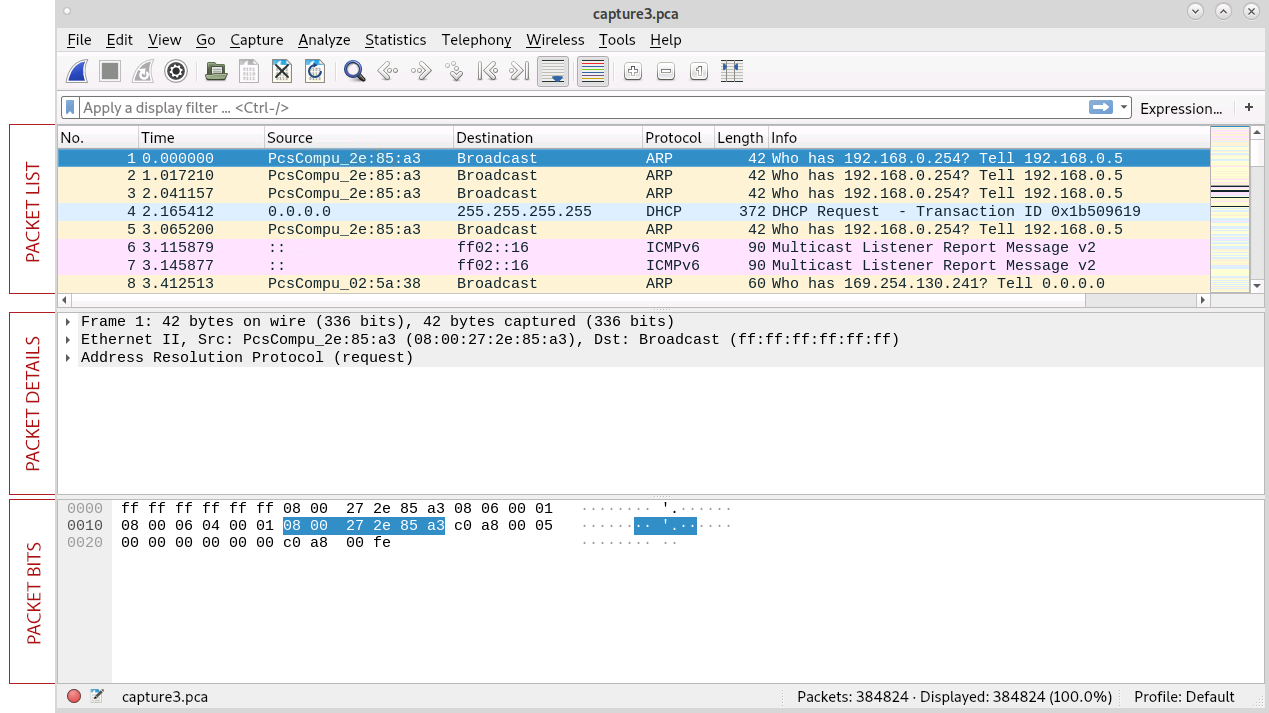
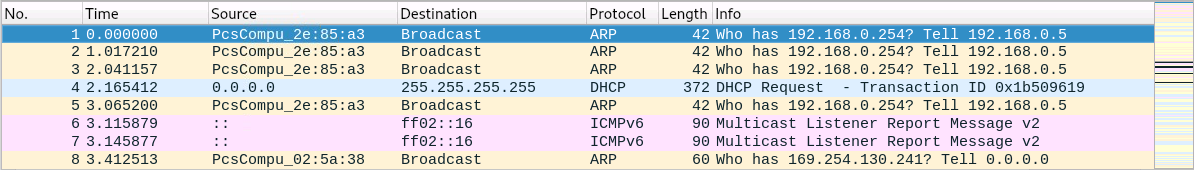
Packet List
The packet list consists of several useful columns populated with key data. As illustrated below, these include to following:
- Time – shows when the packet was captured.
- Source – shows where the packet originated from (IP or other).
- Destination – shows where the packet was heading.
- Protocol – shows the protocol used.
- Length – shows the length of that packet.
- Info – displays any additional information about the packet itself.
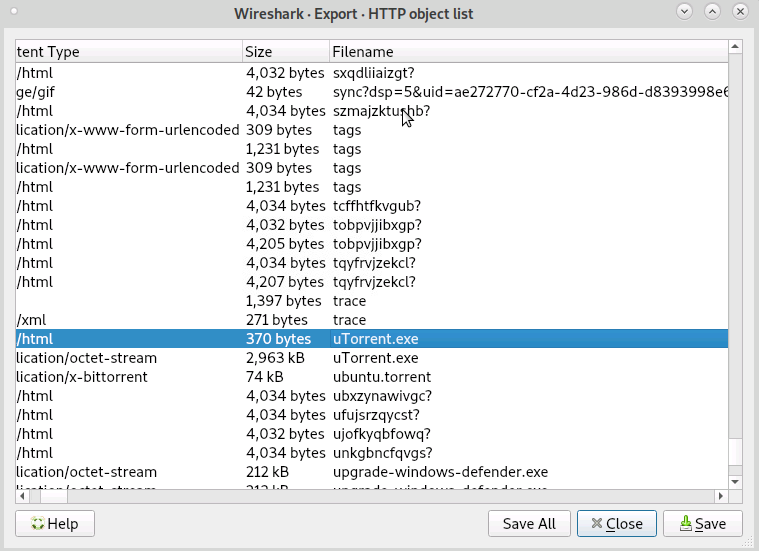
Exporting Data and Files
A handy feature in Wireshark is Export Objects which can be accessed through File -> Export Objects. This allows the user to extract several types of packet data, be it HTTP, SMB, or any other type of object. When exporting a set of objects, users get a list of all of the files that have moved around within the network. This feature also enables users to save those objects into a file. That means users can extract all the files that have been traversing their networks – obviously a very powerful feature.
Filters
Filtering packets in Wireshark is fairly easy and straightforward. Users can write their own filters and combine them in a filter string that meets their needs. For users who aren’t writing their own filters, Wireshark provides the option of using premade filters. This functionality can be accessed by clicking on the blue ribbon on the left-hand side of the filter input field. The following are illustrative examples:
http.request.method == GET # Filter out all GET http requests
!(tcp.port == 22) # Don't show any port 22 (SSH) traffic
tcp portrange 1234-3456 # Capture traffic within a range of ports
src net 10.10.10.0/24 # Capture traffic from a range of IP addresses:
In Conclusion
Wireshark is a useful tool for a wide range of network monitoring tasks. It’s a fun gadget for the enthusiast and a powerful tool for network professionals. This blog post only scratched the surface of what Wireshark is actually capable of. To explore this interesting and powerful system more fully, visit wireshark.org.

